The Growing Risk of Fraudulent Hard Drives — And Why Verification Matters More Than Ever
A recent report by heise article on HDD fraud highlights a concerning reality: fraud involving used hard drives sold as new is not slowing down.

A recent report by heise article on HDD fraud highlights a concerning reality: fraud involving used hard drives sold as new is not slowing down.

If you’ve been following the latest whispers from Silicon Valley and the AI community online, you’ve probably seen chatter about developers snapping up Mac Minis to run local AI agents like the project formerly known as Clawdbot (now going by Moltbot)–a sort of 24/7 autonomous assistant that operates right on your own hardware. The idea is that instead of relying on cloud servers, this agent lives locally, remembers your preferences, and can take actions on your behalf. Mac Minis have become a go-to for this because of their efficient Apple Silicon architecture, small footprint, silent operation, and tight integration with macOS.

Recently, heise online revealed that numerous older Western Digital hard drives — particularly from the Blue, Red, and Purple series — may be on the brink of failure due to firmware vulnerabilities tied to Shingled Magnetic Recording (SMR) technology. SMR stacks data tracks like roof shingles, allowing greater capacity, but at a cost: the firmware must constantly track where each piece of data lives.

When tariffs on imported electronics bite, the reflex isn’t just “pay more or stop buying.” Smart enterprises and ITADs can turn toward refurbished gear as both a shield and an opportunity. Leaning into used and remanufactured devices can reduce cost, stretch lifespans, and reshape the ITAD and reseller landscape — though it also brings new challenges in component sourcing and data security.

In today’s fast-paced IT asset management industry, seamless data exchange between systems is crucial for efficiency, accuracy, and compliance. Securaze has been designed to integrate smoothly with external systems, particularly Enterprise Resource Planning (ERP) platforms, ensuring an automated and streamlined approach to handling asset data.
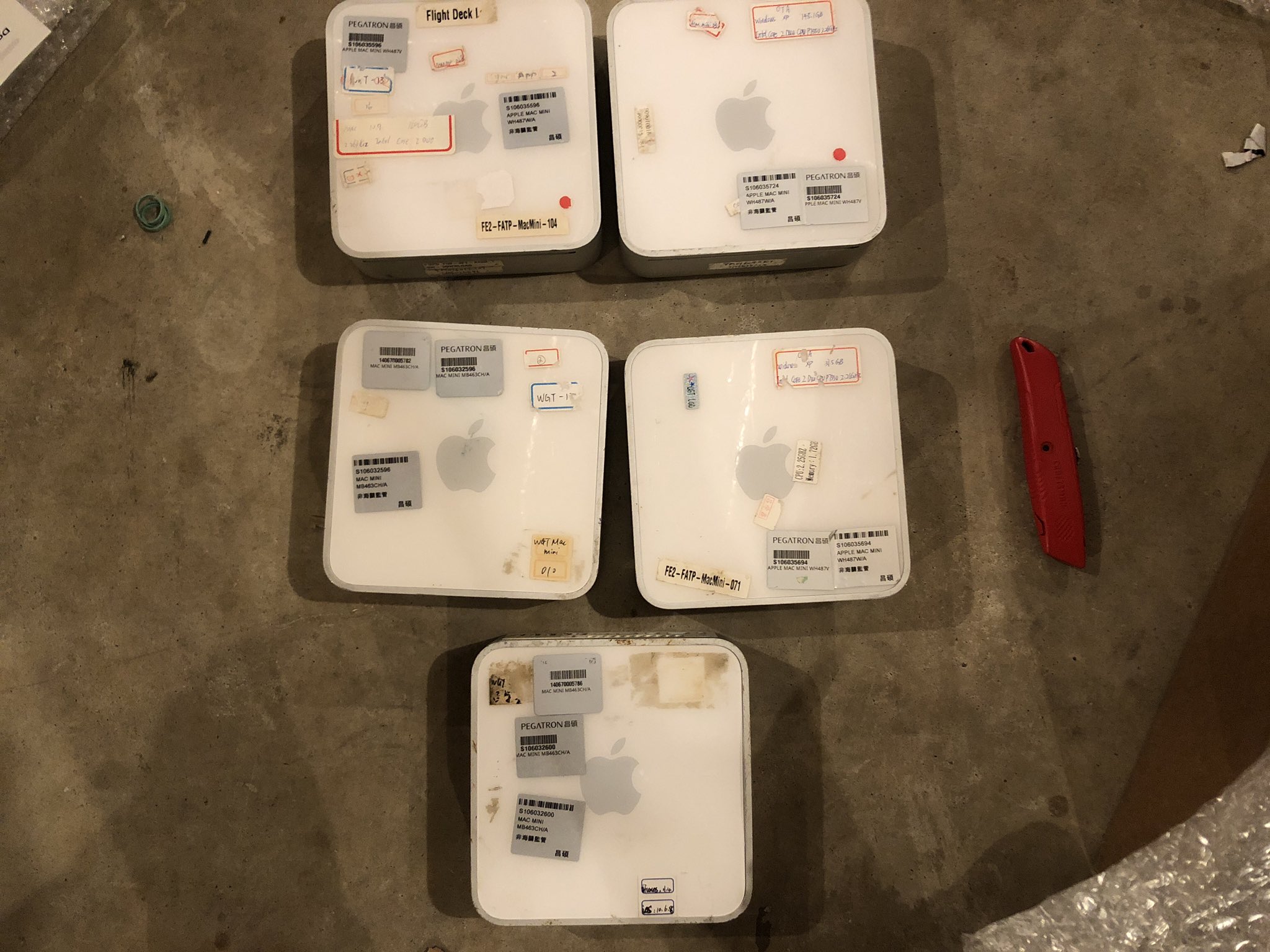
A cautionary tale about recovered software from Mac Minis brought to us by dosdude1 on "X".

The NIS 2 Directive represents a critical step in enhancing cybersecurity across the European Union, particularly in sectors essential to the functioning of society and the economy. Coming into force by October 17, 2024, this directive imposes comprehensive security measures on companies in key sectors, requiring them to strengthen their information systems and protect data from cyber threats. Unlike the GDPR, which applies only to personal data, NIS 2 has broader implications, affecting every company that meets certain thresholds or operates in sectors critical to national infrastructure.
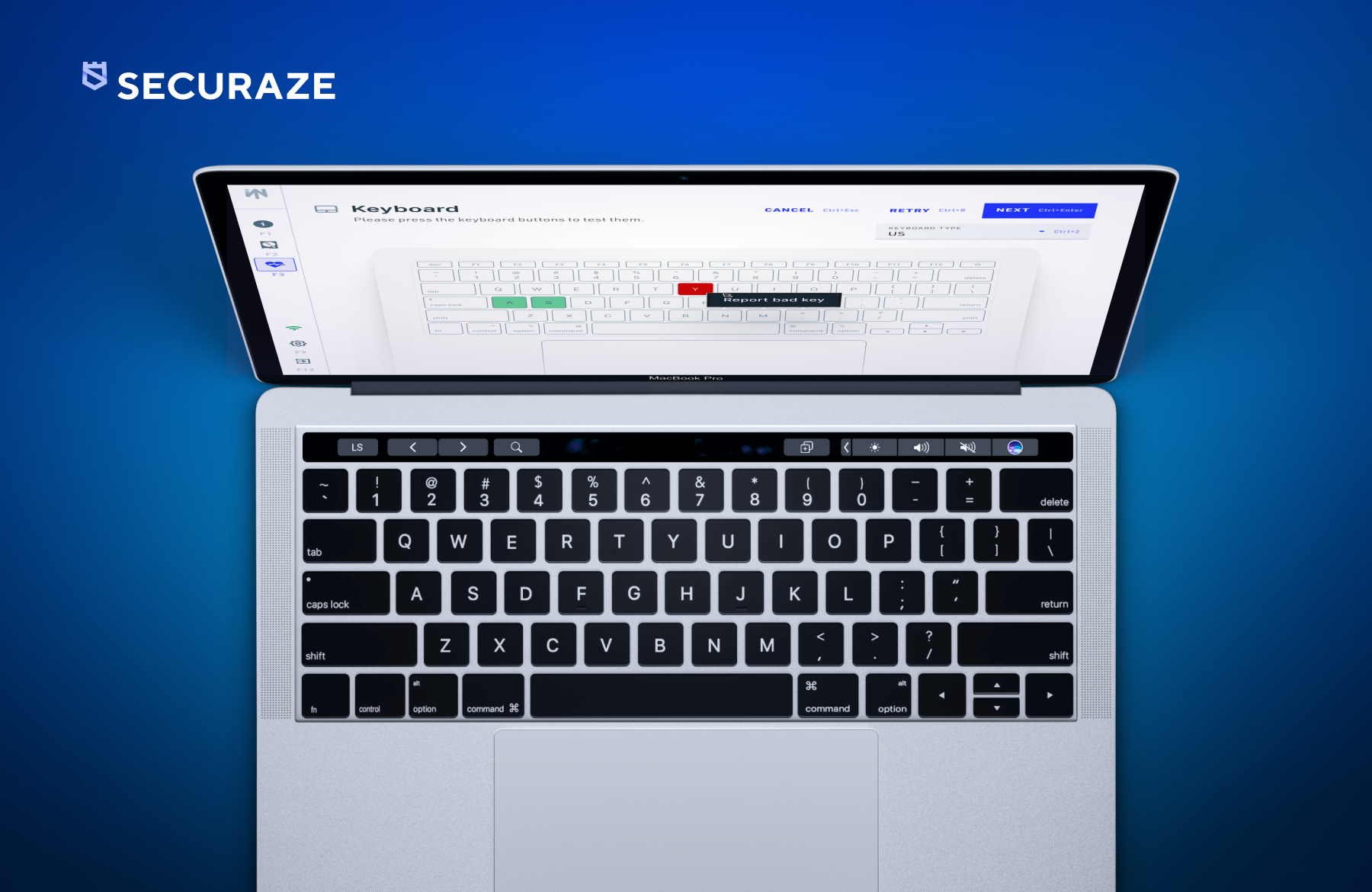
Apple's announcement regarding the imminent end of its butterfly keyboard service program for MacBooks signals a crucial deadline for IT asset disposition (ITAD) and refurbishing businesses. With only 2019 model of the 13-inch MacBook Pro still eligible for free repair, it's imperative for businesses to utilize tools like Securaze Work to capitalize on the remaining opportunities and maximize profits.

Apple has once again captivated tech enthusiasts with its latest announcement: the introduction of the new 13 and 15-inch MacBook Air models featuring the formidable M3 chip. This unveiling marks a significant leap forward in the evolution of Apple's lineup, promising enhanced performance and efficiency for users across the globe.

Securaze is the ONLY one worldwide to have achieved Common Criteria certification for our Mobile Erasure (Android and iOS)!