The Risks of Deleting Without Secure Erasure: Recoverable Data Found on Mac Mini Batch Listed for Sale in China
A cautionary tale about recovered software from Mac Minis brought to us by dosdude1 on "X".
Posts about:
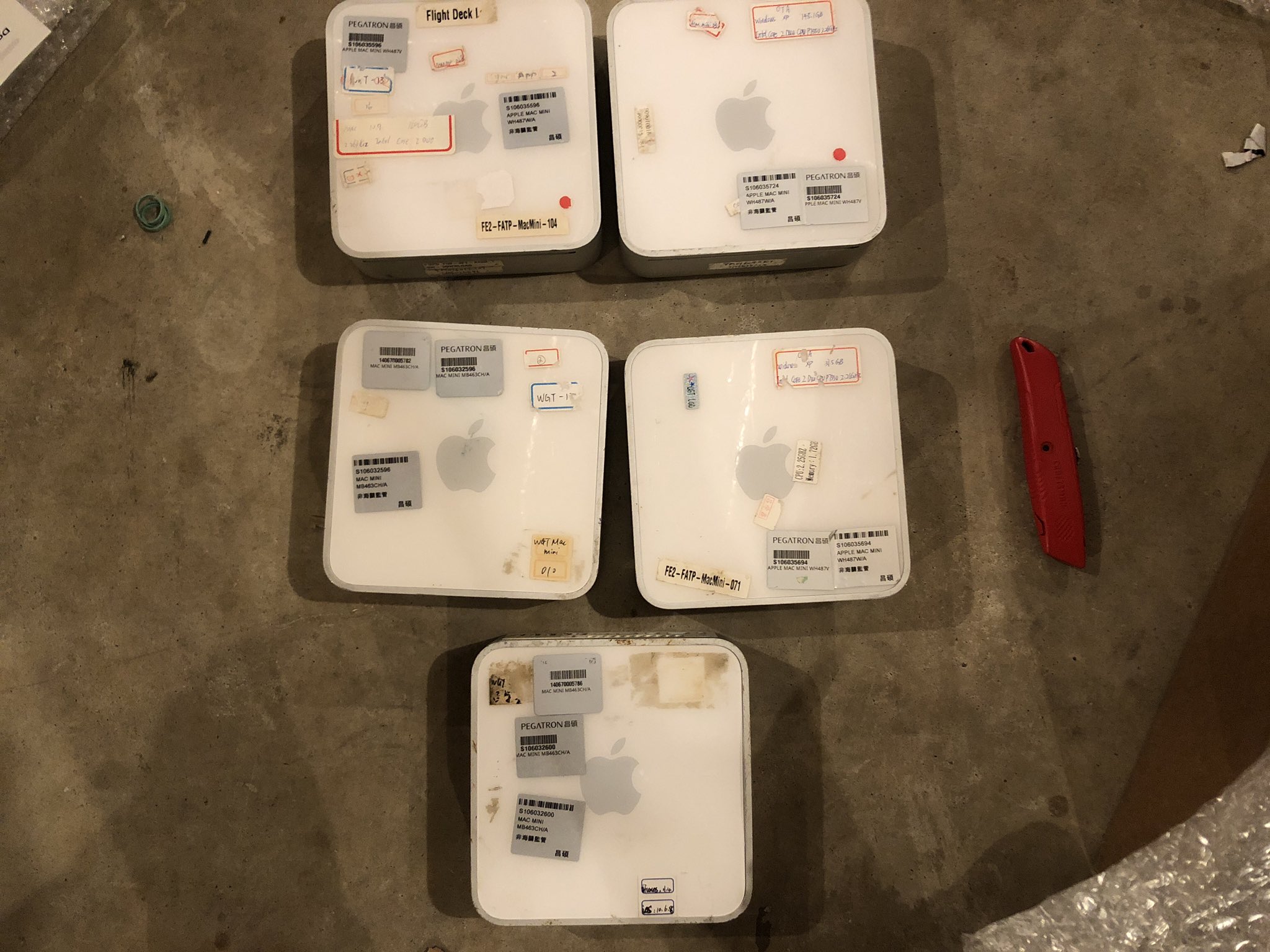
A cautionary tale about recovered software from Mac Minis brought to us by dosdude1 on "X".

In today's rapidly evolving technological landscape, the lifespan of our electronic devices is becoming increasingly shorter. Upgrades are the norm, leading to a surplus of discarded devices. However, simply performing a factory reset before selling or repurposing your device might not be enough to ensure your sensitive data is fully protected. The recent cautionary tale from Canon serves as a stark reminder of the potential risks.

Intoduction
In an age where data breaches and cyber threats are increasingly common, ensuring the security of sensitive information has become a top priority for businesses and individuals. Two primary methods for safeguarding data are encryption and secure erasure. Although both serve the purpose of protecting data, they address different aspects of data security. In this comprehensive guide, we'll explore the ins and outs of encryption and secure erasure to help you determine the best approach for your data protection needs.
.png)
Do your customers request proof of where their devices have been erased? Do they want confirmation that their devices and confidential data have not left the country or ended up in the wrong hands? Are they looking for proof that all aspects of your contract have been fulfilled?