Securaze Mobile & Common Criteria
Securaze is the ONLY one worldwide to have achieved Common Criteria certification for our Mobile Erasure (Android and iOS)!
Posts by

Securaze is the ONLY one worldwide to have achieved Common Criteria certification for our Mobile Erasure (Android and iOS)!

While the tech world was looking forward to the upcoming release of the iPhone 15 in September, an exciting development is taking place in the market which could have a major impact on those consumers who are seeking almost-current smartphones at lower prices. The trend is the market opening up for recycling, remanufacturing and bringing back to the market used iPhone models 13 and 14.
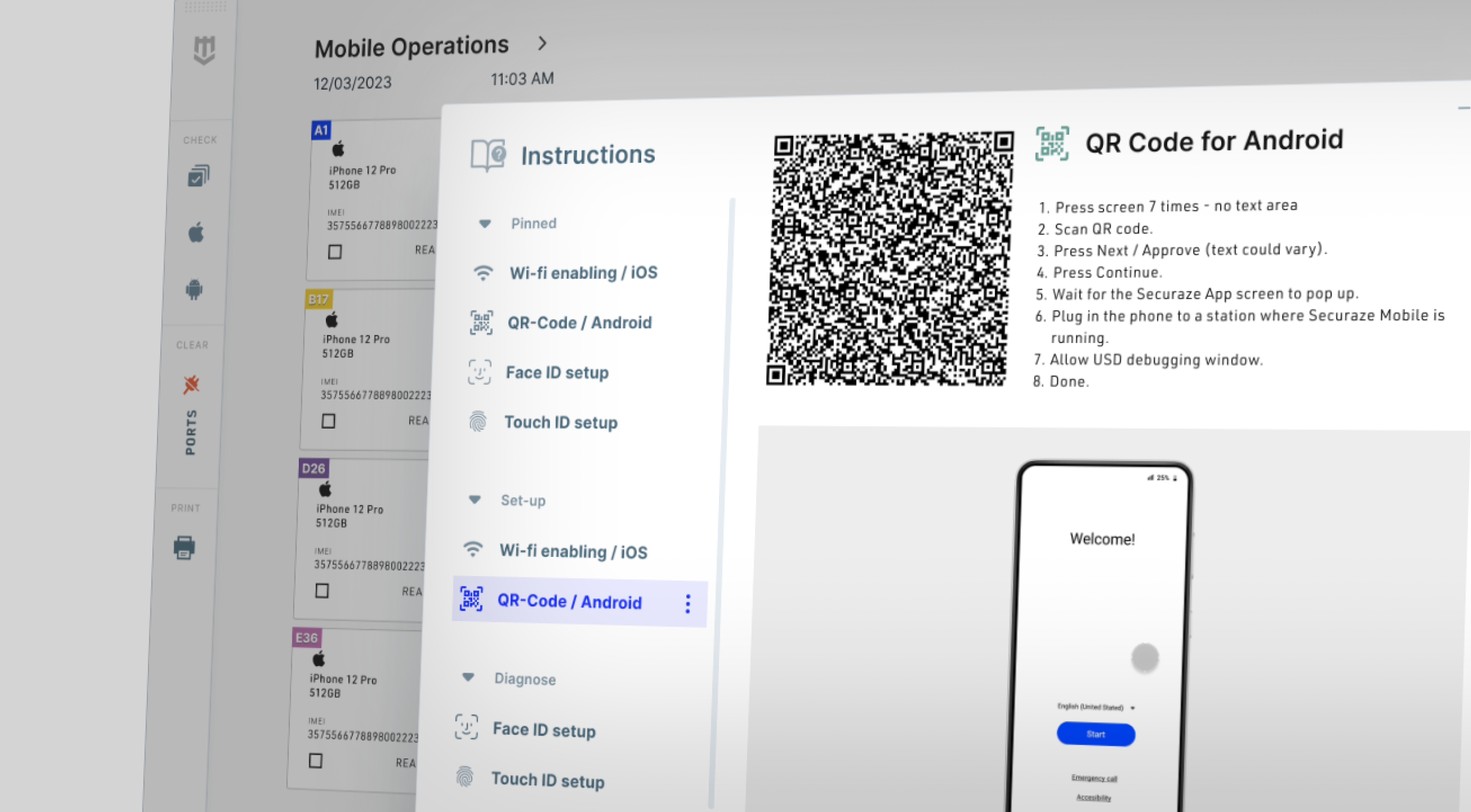
Securaze Mobile has long been synonymous with secure data erasure in the mobile industry. In our relentless pursuit of innovation, we are proud to present the most recent developments in Securaze Mobile, introducing a new era in secure management of your mobile devices.

Mobile phones have undeniably become a fundamental part of our lives, but the constant urge to own the latest model every two to three years has led to rising costs and an increasing ecological impact. However, a positive shift is underway as the demand for used and refurbished mobile devices rises steadily. Not only does this market offer cost-effective options, but it also presents a promising opportunity to make a significant contribution to sustainability.

In today's digital world, our lives are increasingly intertwined with computers and the internet. Whether it's our personal online activities or sensitive work-related information, the data we share holds immense value. However, recent incidents remind us of the risks associated with data loss and exposure. This blog post delves into a noteworthy case involving SAP's data center, emphasizing the critical need for data protection and secure data erasure.

Intoduction
In an age where data breaches and cyber threats are increasingly common, ensuring the security of sensitive information has become a top priority for businesses and individuals. Two primary methods for safeguarding data are encryption and secure erasure. Although both serve the purpose of protecting data, they address different aspects of data security. In this comprehensive guide, we'll explore the ins and outs of encryption and secure erasure to help you determine the best approach for your data protection needs.
.png)
Do your customers request proof of where their devices have been erased? Do they want confirmation that their devices and confidential data have not left the country or ended up in the wrong hands? Are they looking for proof that all aspects of your contract have been fulfilled?
.png)
To ensure data security at the end of an asset's life, data erasure software is an essential tool that completely removes sensitive information from storage devices. To be effective, such software must comply with industry standards, such as those set by the National Institute of Standards and Technology (NIST). This article will explain how Securaze complies with NIST standards.
-1.png)
By now, you’ve likely heard the incredible statistics around E-waste: one of the largest and most complex waste streams in the world, having devastating consequences on everything from sustainability, to health, to geopolitical implications shaping our world.
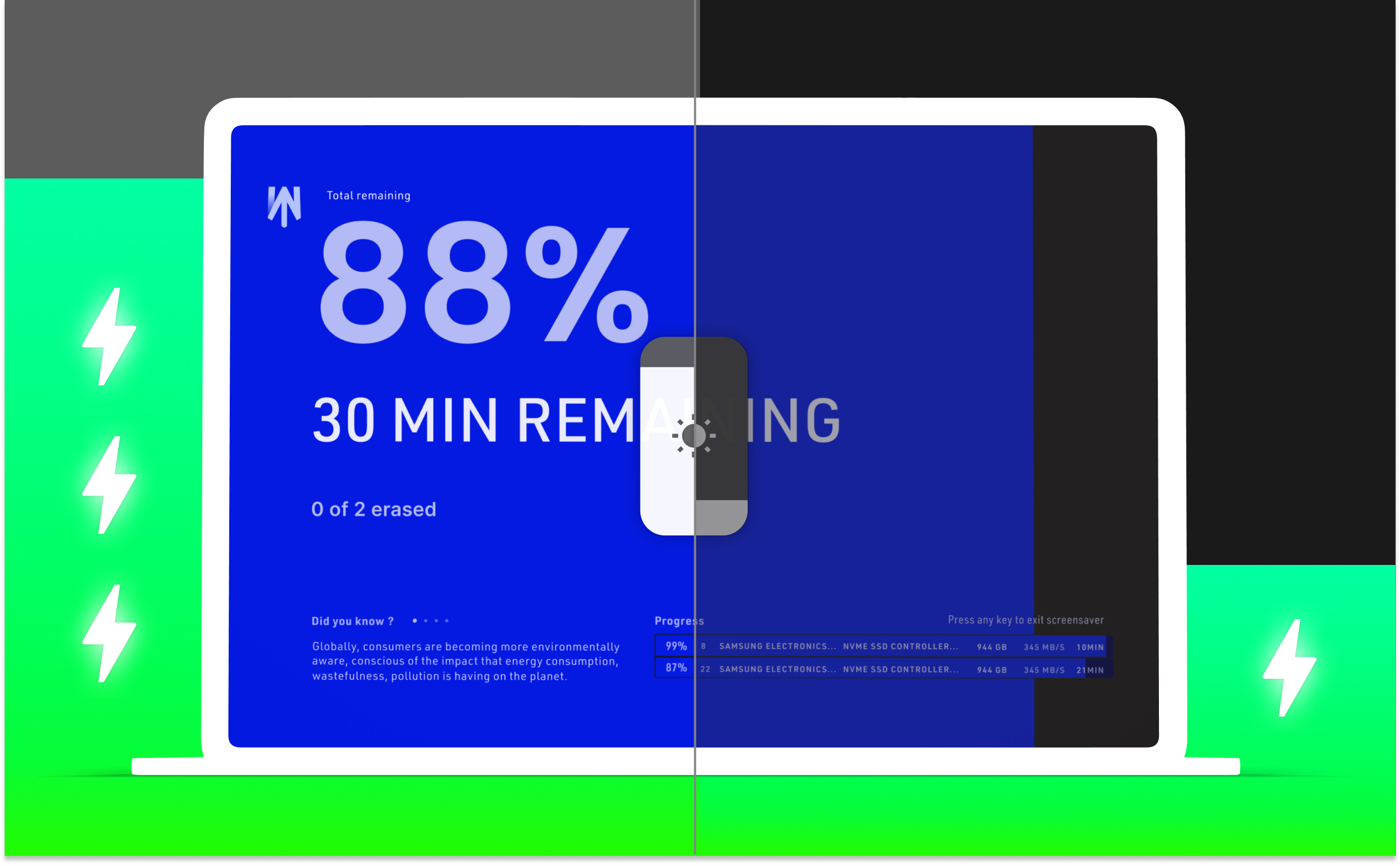
Whether for work, study or leisure, computers have become an indispensable part of everyday life. But intensive use can consume a lot of power, and with rising...